TL;DR
- You face mounting compliance obligations (HIPAA, NYDFS, FINRA) and limited internal security staff; deciding between in-house vs outsourced it compliance is now a risk and budget decision.
- Quick answer: for many regulated NJ/NY firms, outsourcing core monitoring and documented controls to an MSSP is the fastest route to audit-ready security without hiring a full security ops team.

Executive summary — how compliance changes the in-house vs outsource decision
If you run a regulated business in New Jersey or New York, compliance changes the hiring equation. Compliance adds fixed obligations — access controls, audit logs, encryption, documented policies, and timely breach notification — that require consistent engineering and evidence collection. You can buy technology and hire staff, or you can contract an MSSP to operate and document the controls. The choice between in-house vs outsourced it compliance hinges on three realities: staffing depth, evidence and audit-readiness, and continuous monitoring capability.
Example: a small medical billing firm subject to HIPAA often lacks 24/7 security ops; outsourcing gives them EDR and SIEM monitoring that they otherwise couldn’t afford. Quotable summary: "MSSPs can provide enterprise-grade monitoring and documented controls that align with NYDFS and HIPAA expectations without the cost of in-house scale."
Key regulatory frameworks for NJ & NY businesses (HIPAA, NYDFS, FINRA, others)
Regulated entities in NJ and NY commonly face multiple frameworks. HIPAA governs protected health information for covered entities and business associates and requires safeguards like access controls, encryption, and Business Associate Agreements (BAAs). NYDFS 23 NYCRR 500 requires financial institutions to maintain governance, risk assessments, written cybersecurity policies, and formal incident response plans with reporting to the regulator. FINRA sets rules for broker-dealers focused on recordkeeping, supervision, and reasonably designed systems to protect client data. Other rules (e.g., PCI DSS for payment card data) may also apply. For more on this, see It cybersecurity solutions.
These frameworks converge on common IT expectations: enforce least privilege, keep immutable logs, demonstrate encryption at rest and in transit, and test response plans. For hipaa it outsourcing nj and nydfs it requirements msp searches, emphasize that each regime expects documented controls and proof they operate in production.
What each regulation typically requires from IT and security teams
HIPAA requires technical safeguards: unique user IDs, access logging, audit trails, encryption where feasible, and BAAs for vendors handling PHI. NYDFS requires governance and reporting: annual risk assessments, a designated Chief Information Security Officer or equivalent responsibility, and rapid reporting of incidents. FINRA expects retention of electronic records and supervisory systems that prevent misconduct. Practically, IT must provide role-based access controls, centralized logging (SIEM), endpoint detection and response (EDR), encrypted backups, and documented incident response playbooks.
Actionable example: a small healthcare practice must sign a BAA with any vendor that processes PHI and demonstrate that EDR events are logged and reviewed weekly. For hipaa it outsourcing nj, an MSSP should be able to provide a BAA, logging exports, and weekly SOC summaries.
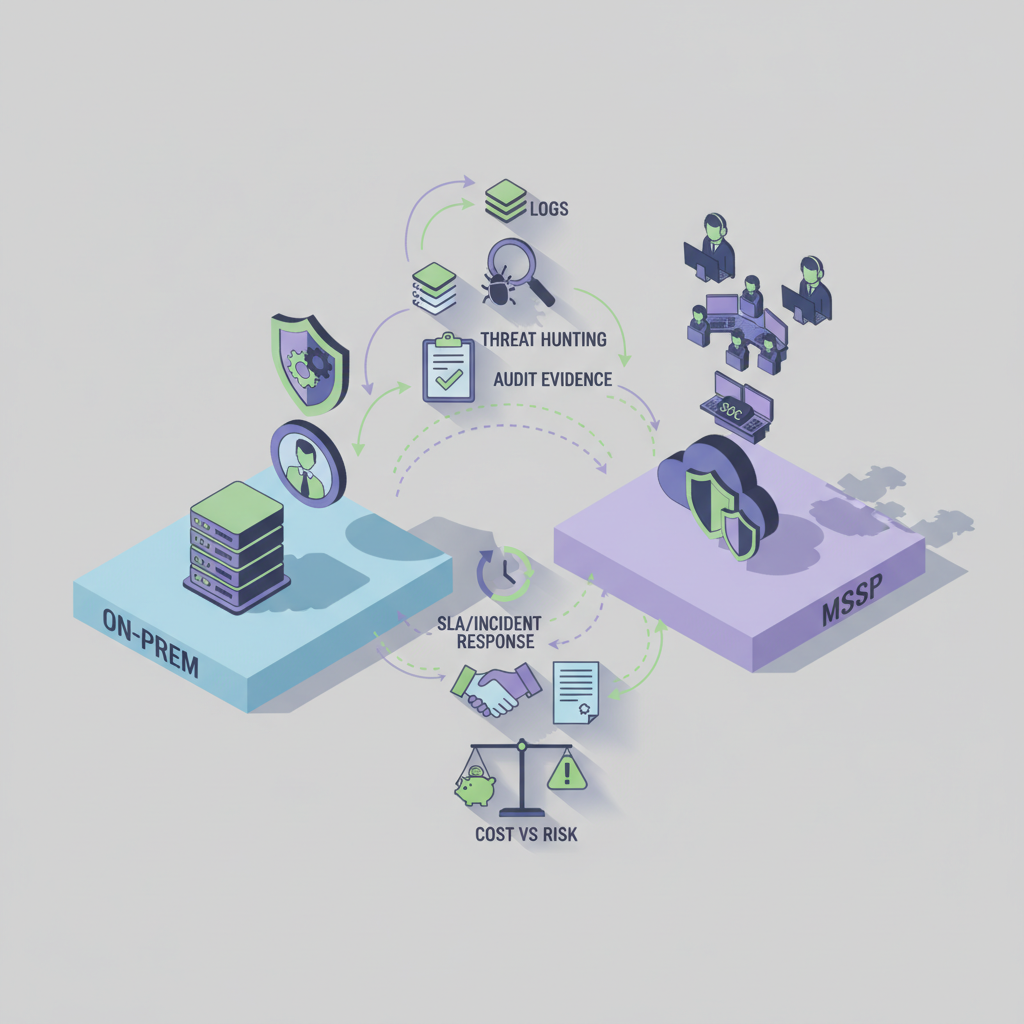
Security capabilities comparison: in-house vs MSSP (EDR, SIEM, threat hunting, zero-trust)
An internal team can be highly effective when staffed and funded properly, but the marginal cost of matching MSSP scale is high. In-house must provision EDR agents, maintain a SIEM, fund threat-hunting expertise, and implement zero-trust controls — and do that 24/7. MSSPs amortize those costs across clients and deliver continuous monitoring, alert triage, threat hunting, and policy tuning.
Concrete thresholds: for many SaaS and small-regulated shops, target EDR coverage of 100% endpoints, SIEM retention of 90 days for high-fidelity logs, and weekly threat-hunting summaries. Real example: a financial compliance team relying on an MSSP gains daily SIEM alerts and monthly forensic reports without hiring three senior analysts. Searchers looking for outsourced security for regulated business will find MSSPs useful where staffing or budget block internal scale.
Enterprise-grade security requires continuous detection, not periodic checks.
Audit-readiness and documentation: who maintains evidence for compliance?
Audit-readiness is the single largest differentiator. In-house teams must keep documented policies, patch records, access logs, change control tickets, and evidence of testing. An MSSP should provide mapped evidence: policy templates, SIEM exports, EDR incident timelines, and periodic compliance reports. The regulator cares that controls exist and that evidence shows they run.
Specific artifact checklist for auditors: (1) role assignments and access-control lists, (2) SIEM log extracts for the audit window, (3) EDR incident tickets with remediation timestamps, (4) encrypted backup logs and restore tests. When considering nydfs it requirements msp or hipaa it outsourcing nj, require the vendor to produce these artifacts on demand and document responsibilities in the contract.
Audit evidence must be reproducible and dated; snapshots beat recollections.
Incident response and breach notification: SLA expectations and real-world timelines
Regulators demand timely detection, containment, and notification. NYDFS expects timely reporting to the superintendent; HIPAA requires notification to affected individuals and HHS depending on breach size and risk. SLAs should cover detection time (MTTD), response time (MTTR), and escalation procedures. Real-world timelines: detection within hours, containment within 24–72 hours, and notifications as required by the regulation. Avoid promising specific guaranteed minutes or hours unless the vendor documents them.
Operational rule: map which party notifies regulators and who prepares the forensic packet. For outsourced security for regulated business, ensure the MSSP provides incident timelines, forensic evidence, and a playbook tied to regulatory deadlines.
Vendor management and third-party risk — MSP contractual controls and attestations
Vendor management is itself a regulatory expectation. Contracts must define responsibilities (who maintains backups, who alerts on incidents), security requirements, and data handling rules. Ask vendors for attestations: SOC 2 Type II reports, penetration test summaries, and BAAs for HIPAA work. For nydfs it requirements msp searches, documentation of vendor oversight and supply-chain risk management is often requested.
Example contract terms to request: right-to-audit clauses, incident notification timelines, encryption requirements, and subprocessor lists. If you outsource, include periodic third-party risk reviews and require evidence that the MSSP enforces zero-trust segmentation and least privilege across its tooling.
Cost vs risk tradeoffs for regulated entities
Cost comparisons must include headcount, tooling, training, and opportunity cost. Hiring junior engineers plus buying point tools often underdelivers relative to an MSSP that bundles EDR, SIEM, and 24/7 monitoring. Risk tradeoffs include residual risk from slower detection, potential fines for compliance lapses, and the indirect cost of a breach.
Concrete decision rule: if your in-house security spend (headcount + tools + training) is less than 60–70% of an MSSP quote but still lacks 24/7 capability, outsourcing is often the safer choice. For firms weighing mssp compliance advantages, factor in the MSSP's documented controls, incident support, and access to senior engineering resources that would cost far more to hire directly.
Decision matrix: when a regulated NJ/NY business should outsource
Use a simple scoring approach: rate Staffing, Budget, Regulatory Complexity, and Required Coverage each 1–5. Total scores ≤10 suggest keep in-house; scores 11–15 consider hybrid; 16+ recommend outsourcing. This decision matrix converts subjective factors into a repeatable rule.
| Factor | Score 1–5 | Guidance |
|---|---|---|
| Staffing depth | 1–5 | Low = outsource |
| Budget | 1–5 | Low budget but high risk = outsource |
| Regulatory complexity | 1–5 | Multiple regimes (HIPAA+NYDFS) = outsource |
| Required coverage (24/7) | 1–5 | 24/7 needed = outsource |
Practical onboarding checklist for a regulated business moving to an MSSP
Onboarding must prioritize evidence mapping, data flows, and urgent controls. Start with a scoping call, sign necessary agreements (BAA if HIPAA applies), run a discovery for assets, and deploy EDR agents and SIEM collectors. Establish escalation contacts and run a tabletop incident exercise within 30 days.
| Step | Detail |
|---|---|
| 1. Contract & BAAs | Execute contract with clear responsibilities and BAAs if handling PHI |
| 2. Asset discovery | Inventory servers, endpoints, cloud services, and data stores |
| 3. Deploy agents | Install EDR and SIEM collectors across all in-scope systems |
| 4. Tune alerts | Reduce false positives and define escalation thresholds |
| 5. Tabletop | Run an incident simulation and produce a remediation plan |
FAQ: common compliance questions
What is compliance & security? Compliance and security are the set of policies, technical controls, documented evidence, and operational processes that ensure an organization meets legal and regulatory requirements while protecting data and systems. This definition frames the choice between in-house and outsourced solutions in IT compliance as both technical and documentary, highlighting the importance of understanding business technology management options.
How does compliance & security work? Compliance and security work through layered controls: preventive (access controls, encryption), detective (SIEM, EDR), corrective (patching, backups), and organizational (policies, training, vendor contracts), combined with documented evidence and regular testing.
Conclusion and next steps (offer free compliance-focused IT assessment)
Deciding between in-house vs outsourced it compliance requires mapping staff, cost, and regulatory obligations to the evidence and monitoring you must produce. If you manage HIPAA obligations or face NYDFS expectations, outsourcing core monitoring and evidence collection often reduces risk and speeds audit readiness. For concrete next steps, run a 30–60 minute compliance-focused IT assessment to map gaps and costs.
Learn about tailored support and how these capabilities can be delivered by reviewing our services or scheduling a demo at our services. To start the assessment, contact us, visit contact us, or use the contact us page.
References
- Guidance on HIPAA & Cloud Computing — U.S. Department of Health & Human Services
- Business Associate Contracts — U.S. Department of Health & Human Services
- 23 NYCRR 500 (NYDFS Cybersecurity Requirements) — New York State Department of Financial Services
- Cybersecurity supply chain risk management practices — NIST
- CISA and NSA cloud security best practices — CISA