TL;DR
- A hybrid IT model (hybrid it model msp) pairs your internal team with an MSP to deliver continuous operations and specialized skills.
- Design clear SLAs, shared tooling, and responsibility matrices to avoid gaps — target uptime, MTTD and MTTR KPIs up front.
- Use co-managed it services for 24/7 coverage while keeping control of business-critical assets; include senior-engineer-led support msp for complex incidents.
- Follow a phased onboarding checklist and local NJ/NY considerations (permits, on-site ratio, staffing windows) before switching to co-management.

The hybrid it model msp combines your in-house team with an external managed service provider to deliver continuous operations, specialist skills, and scalable coverage. This guide walks you through what co-management looks like, the business benefits, the practical splits of responsibility, SLAs and workflows, recommended tooling, hiring guidance, onboarding artifacts, an anonymized NJ/NY case-study template, and governance considerations.
What is a hybrid / co-managed IT model? Quick definition
Co-managed IT (sometimes called hybrid IT) is a shared operational model where an internal IT team and an MSP operate the environment together under defined responsibilities. A concise definition: "Co-managed IT means retained internal control of strategic systems, combined with outsourced operational coverage for monitoring, escalation, and specialist tasks." For more on this, see In-house vs outsourced technology management.
A concrete example: an SMB employs an in-house systems administrator to handle daily user support and application configuration, while the MSP offers 24/7 monitoring, patch orchestration, and incident escalation. This MSP delivers senior-engineer-led support for complex server recoveries or security incident response, allowing the in-house team to maintain ownership of business rules and privileged access. This collaboration highlights the importance of understanding IT and cybersecurity solutions for effective management.
Quotable fact: "Co-managed IT lets businesses keep institutional knowledge locally while outsourcing monitoring and specialist tasks to an MSP."
Business benefits: coverage, scalability, access to senior engineers
A hybrid it model msp delivers three measurable business benefits: continuous coverage, elastic capacity, and access to senior expertise. Continuous coverage: you gain 24/7 incident detection and response without forcing internal staff into night shifts. Elastic capacity: the MSP scales monitoring, backup, and project resources during peaks. Senior expertise: your team can escalate to senior-engineer-led support msp resources for forensic analysis, complex migrations, and ransomware recovery planning.
Specific outcomes executives care about: uptime targets, MTTD (mean time to detect), MTTR (mean time to recover), and ticket SLA compliance. Example KPI set for executives (quotable): "Target 99.9% core service uptime, MTTD under 15 minutes, MTTR under 4 hours for P1s, and 95% ticket SLA compliance." Use these figures as starting points and adapt by application criticality.
Co-management succeeds when responsibilities are explicit, tooling is shared, and escalation routes are fast and tested.
Typical co-managed service models and responsibilities (helpdesk, security, projects)
Co-managed arrangements differ by focus. Typical models include: helpdesk-first co-management where the MSP handles after-hours and overflow tickets; security-first co-management where the MSP runs EDR and SIEM monitoring while internal staff handle policy and exceptions; and project-based co-management where the MSP provides project leads for major upgrades while the internal team retains acceptance testing.
"Practical responsibility examples: helpdesk — internal team handles first-contact during business hours; MSP manages after-hours and ticket triage; security — internal team owns identity lifecycle and privileged accounts, while MSP oversees incident monitoring, threat hunting, and alerts; projects — internal product owners define scope, and MSP assigns senior engineers for execution. For any inquiries, feel free to contact us."
Mentioning co-managed it services and managed services and in-house it in the same policy document avoids overlap: include an RACI (Responsible, Accountable, Consulted, Informed) for each service area and test it with three simulated incidents.
Example splits of responsibility (SMB, mid-market, regulated)
SMB: The MSP runs 24/7 monitoring and patching, internal IT handles local printer and desktop issues. Mid-market: internal teams retain server and application ownership; MSP provides SIEM, backups, and senior-engineer-led support msp for escalations. Regulated industries: internal staff keep compliance controls and audit evidence; MSP implements technical controls (EDR, backups) and provides forensic support when required.
Decision rule: if a task involves business logic or privileged workflows, prefer internal ownership; if it requires continuous monitoring or specialized incident response, assign to the MSP. Example threshold: if a service outage affects >20% of users or a regulated dataset, escalate to MSP P1 workflow immediately.
How to design SLAs and workflows between in-house staff and an MSP
Start SLAs with measurable targets and an escalation ladder. Key SLA items: detection time (MTTD), response time (time-to-start remediation), ticket resolution SLA by severity, and periodic review cadence. Example SLA table row: P1 (business down) — MTTD 15 minutes, response start 30 minutes, joint incident call within 60 minutes.
Workflow practices: use a shared ticket queue, agree on priority mapping, define who opens public communications, and schedule weekly ops syncs. Include runbooks for the top 10 incidents. Practical rule: require a joint tabletop exercise every six months to validate roles and update SLAs based on measured MTTD/MTTR.
An SLA is only useful when it includes clear escalation steps and a tested incident playbook.
Tools and integrations (RMM, ticketing, SIEM) required for smooth co-management
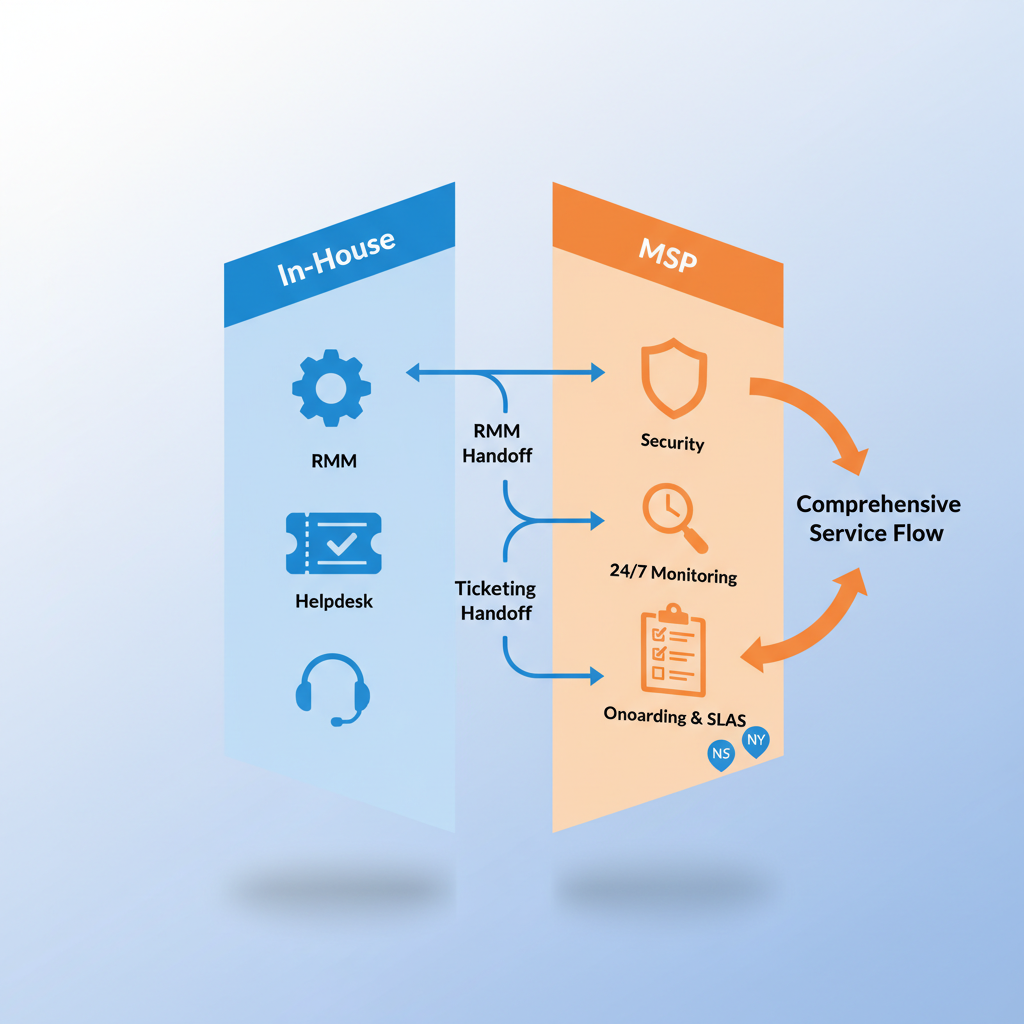
Shared tooling is the backbone of co-management. Minimum stack: remote monitoring and management (RMM) for endpoint health, a shared ticketing system with role-based access, and a SIEM for centralized security telemetry. Integrations needed: RMM alerts into ticketing, SIEM alerts into the MSP console, and backup verification alerts to both parties.
Concrete example: push RMM agent health alerts into the shared queue with priority mapping, forward SIEM high-severity alerts to the MSP SOC and to an internal security contact, and define automated backup verification reports weekly. For NJ/NY companies, include local on-site maintenance windows in ticketing rules to align with regional staffing constraints.
Share one source of truth for alerts and tickets to avoid duplicated work and blind handoffs.
Hiring and role recommendations for internal teams in a co-managed setup
Hire roles that preserve strategic control and act as the MSP liaison: an IT operations lead, a security governance owner, and a systems integrator who understands business workflows. The operations lead owns daily triage and acceptance testing of MSP work. The security owner keeps compliance evidence and approves changes. The systems integrator manages application-level configuration that the MSP should not change without approval.
Staffing guidelines: for small orgs, a single IT generalist plus MSP is common; for mid-market, keep at least one senior systems engineer to work with senior-engineer-led support msp resources. Decision threshold: if you need to approve privileged actions within minutes during business hours, keep that role in-house.
Onboarding checklist and timeline for transitioning to hybrid IT
Onboarding should be phased and documented. Use this checklist:
- Inventory assets and owners (network, servers, SaaS, backups)
- Map responsibilities into an RACI and agree on SLAs
- Deploy and verify shared tooling (RMM, ticketing, SIEM)
- Run two-week parallel operations window (MSP and internal team operate simultaneously)
- Conduct a tabletop incident simulation and adjust runbooks
| Phase | Duration | Key deliverable |
|---|---|---|
| Discovery | 1–2 weeks | Complete asset inventory |
| Integration | 2–4 weeks | Tooling & RACI implemented |
| Validation | 2 weeks | Parallel ops & tabletop |
Timeline rule: require at least one full incident test before moving to managed-only operations.
Real-world case study template (anonymized NJ/NY example) and KPIs to track
Case study template: organization type, challenge, chosen split of responsibilities, tooling used, onboarding timeline, outcomes, and KPIs. Example (anonymized NJ/NY firm): mid-market finance firm; challenge: no after-hours monitoring and insufficient security staff; solution: co-managed it services with MSP providing SIEM and 24/7 monitoring while in-house retained compliance controls; outcome: MTTD improved from days to under 30 minutes and audited backups restored within policy windows.
KPIs to track (quotable short set): uptime, MTTD, MTTR, ticket SLA compliance, backup recovery success rate. Example targets to evaluate: P95 application latency <200ms, backup restore test success 100% in quarterly checks.
Cost, governance, and security considerations
Cost model: combine fixed monthly fees for monitoring with variable project hours; compare that blended cost to hiring a full internal night-shift engineer. Governance: require joint change approval for privileged changes, maintain an access matrix, and schedule quarterly review meetings. Security: preserve least-privilege access for MSP accounts, log all privileged sessions, and require MSP incident reports for any P1 event.
Regulatory note for NJ/NY firms: ensure the MSP can support required audit logs and that data residency requirements are met. When negotiating contracts, include post-termination access and data handoff clauses.
FAQ: common implementation concerns
What does it mean to build a hybrid (co-managed) IT model? Building a hybrid IT model means pairing retained internal IT responsibilities with outsourced operational coverage from an MSP, documented with SLAs, shared tooling, and joint runbooks.
How do you build a hybrid (co-managed) IT model? Build a hybrid model by inventorying assets, assigning RACI, deploying shared monitoring and ticketing, signing SLAs with escalation steps, and running a phased parallel operations period with tabletop exercises.
When not to build a hybrid (co-managed) IT model
- If your business must keep all operations on-premises and cannot grant remote MSP access under any circumstances.
- If you lack any internal IT resource to act as a liaison; co-management needs at least one internal owner.
- If regulatory rules explicitly prohibit third-party access to sensitive systems and no compensating controls are allowed.
- If your environment is extremely small and the cost of coordination exceeds the value of added coverage.
Conclusion and next steps (schedule co-managed readiness assessment)
Moving to a hybrid it model msp gives NJ/NY organizations 24/7 coverage, access to senior-engineer-led support msp resources, and scalable operational capacity while keeping internal control. Next steps: use the onboarding checklist, run a two-week parallel validation, and set executive KPIs (uptime, MTTD, MTTR, ticket SLA compliance) for the first 90 days.
To explore co-managed it services and how they integrate with your managed services and in-house it team, review our services or schedule a demo at our services. For direct inquiries, contact us or visit the company site at contact us.

